The trouble with lead generation is that in itself, it means nothing.
You could buy a lead list, turn to your phone contacts, or drive ad traffic to a landing page all you want and still end up with little to no results.
There are many factors that contribute to this. But, one rather persisting reason is lead quality.
It’s hard, if not impossible, to know who your next buyer is.
Or is it?
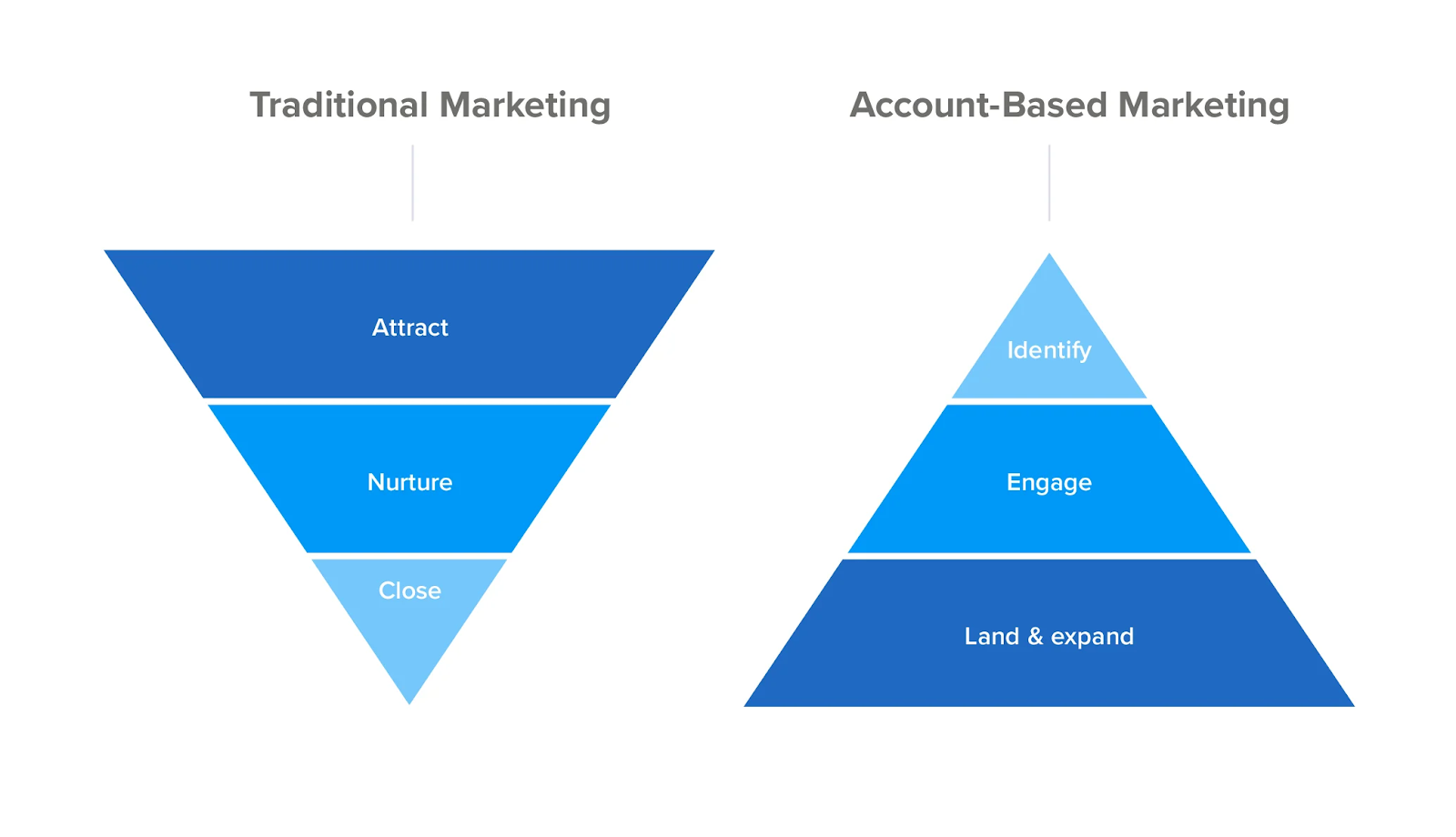
Account-based marketing (ABM) attempts to turn typical marketing and lead generation on its head. It does so by first identifying high-quality prospects, and then approaching them with targeted content.
ABM has a lot of potential for cybersecurity lead generation. As cybersecurity marketing campaigns increasingly focus on chief security officers (CSOs), a highly customized approach will be required.
In this article we’ll break down exactly what ABM is and how it can take your cybersecurity business’ lead generation efforts to new heights.
Scale insightful marketing content across the web.
We help you grow through expertise, strategy, and the best content on the web.
What is Account-Based Marketing?
Weeding through a long list of leads is a waste of time. You’d rather be talking to the people who you know have a high probability of converting, which is what ABM is all about.
ABM is a highly personalized approach which focuses on creating highly personalized marketing campaigns for each account. ABM essentially flips traditional marketing on its head.
While traditional marketing tries to find ideal customers from a large pool of candidates, an ABM campaign zeroes down on the perfect candidates right at the start.
In short, ABM is about as “spend the first four hours sharpening your axe” as it gets in the marketing world — and boy is it effective!
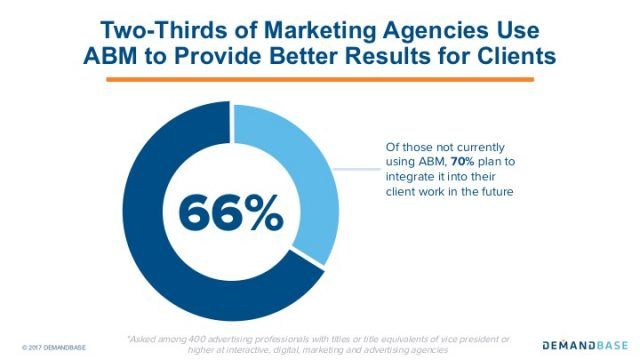
ABM has risen in B2B marketing circles partly because it can put regular lead generation on steroids.
It’s also helping companies generate an average of 208% more revenue with their marketing efforts.
The best account-based programs return a 75% increase in all commodity volume (ACV) and a 150% appreciation in loan to value ratio (LTV) if done right.
Simply put, ABM offers the best chance for a cybersecurity lead generation program to get it right the first time.
ABM comes in three flavors…
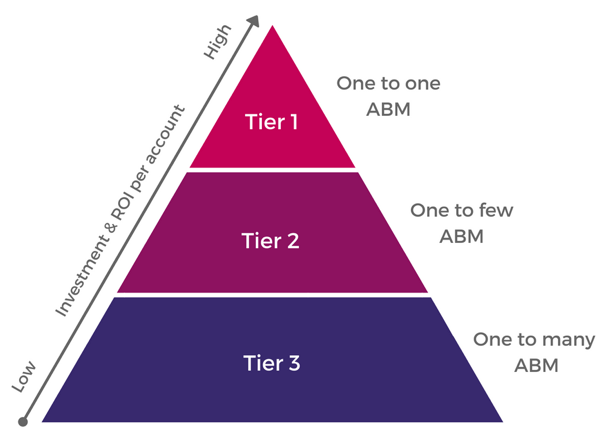
One-to-One ABM
The topmost tier will consist of accounts that fit your ideal buyer persona perfectly. As accounts here will be your most valuable prospects, they should be treated with a highly personalized and bespoke manner.
A typical one-to-one ABM strategy will target around 10 key accounts that have a high probability of impacting your yearly revenue significantly.
One-to-one ABM makes sense if:
- You have access to a lot of information about the target account.
- Your accounts have several stakeholders needed for buy-in.
- Your product fits perfectly into the account’s tech stack.
- Your product has unique features that the account needs.
- You can create highly targeted content for each of your one-to-one accounts.
One-to-Few ABM
AKA ABM Lite, a one-to-few strategy that affects personalization across a larger set of accounts. You should group these accounts by markets or sub-niches within a market.
So, let’s say you provide endpoint security services to the healthcare sector. Your cybersecurity lead generation campaign can target accounts in pharmaceuticals, medical devices like X-Ray machines, and health insurance.
ABM Lite makes sense if:
- You have a small group of target accounts.
- You need to get buy-in from three to five stakeholders.
- You can create niche-specific content.
One-to-Many ABM
There will be accounts that seem like a good fit, but don’t check as many boxes. This is where one-to-many ABM can help you.
The International Technology Services Marketing Association or ITSMA considers the ideal number of accounts in one-to-many campaigns to be 100. But, feel free to go with a number you’re comfortable with.
One-to-many campaigns make sense if:
- You want to build brand awareness.
- Your product is new.
- You don’t have enough information on your ideal target audience.
- You are looking for a faster ROI.
How to Integrate ABM into Your Cybersecurity Lead Generation Strategy
ABM can seem intimidating at first glance. But, a measured and deliberate strategy can help you turn it into a powerful cybersecurity Lead Generation software.
In fact, companies report ABM strategies result in 71% greater ROI than other marketing methods.
Here are a few strategies to help you get started:
Strategy #1: Define and find your target accounts
The Ideal Customer Profile (ICP) is essentially an account level buyer persona. It describes a fictional organization that has the greatest need for your products or services.
An ICP should include your ideal client’s…
- Industry
- Number of employees
- Budget
- Revenue
- Customer base
- Technology stack
- Level of organizational and technological maturity
Feel free to choose the metrics that best fit your lead generation goals. Once finished, you will have a better idea of what to look for in your ideal accounts.
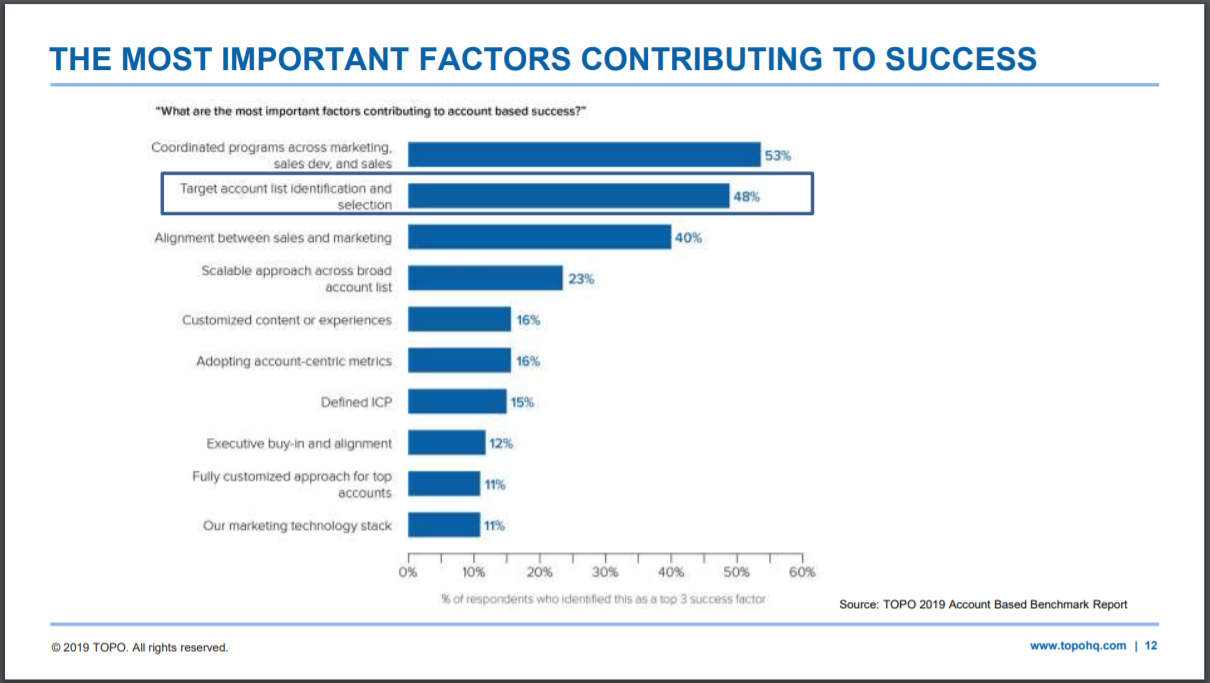
Now, let’s find some accounts that fit your data-driven ICP. Don’t hurriedly skip over your list and fill it up at random though. Target account choice is of make-or-break importance to your ABM efforts.
A few choices you can look into:
Your Database
Harrowing as it may sound, sales often ignore 80% of marketing qualified leads. Now will be a good time to see if that might be true in your case! Map all the leads in your database against your ICP and see how many boxes each of them tick.
Your Competitor’s Clients
You can use tools like Enlyft to research your competition. Alternatively, looking for recommendations and followers on LinkedIn, case studies, and testimonials on a competitor’s website can help you generate more leads, too.
Your Client’s Competitors
CrunchBase and Alexa can help you find companies like those of your existing clients.
Strategy #2: Tier accounts based on how closely they fit the ICP
By now you should have a nice list of target accounts in your ABM database. Your next challenge is to tier all of them based on how well they fit your ICP.
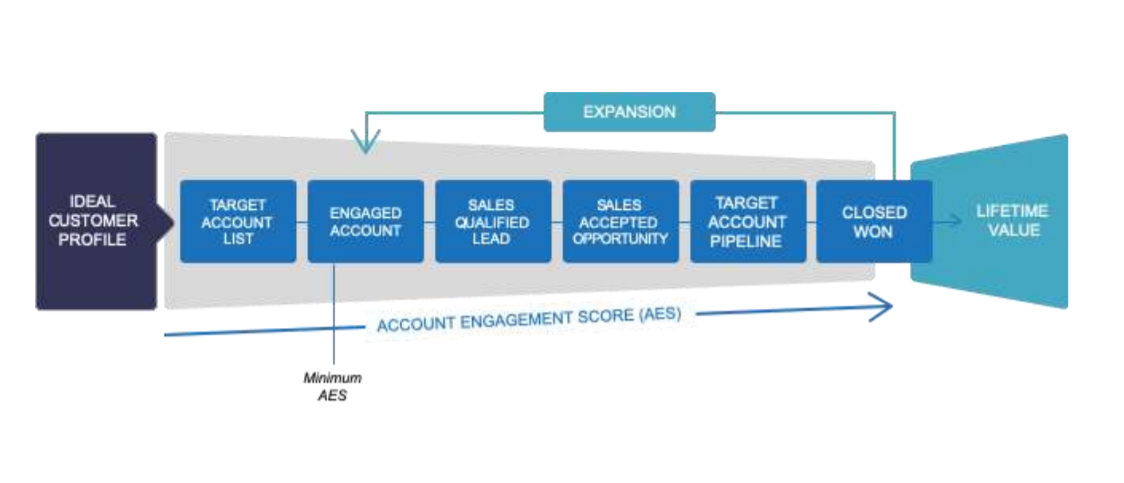
Consider using an Account Engagement Score (AES) to measure how well an account responds to your ABM initiative. So, a minimum AES can be assigned to an account that has engaged with your content, while the highest AES will go to a won account.
Tiering helps you decide how to allocate your resources among your target accounts.
Tier 1 Accounts
These accounts fit your ICP perfectly and should be treated with a bespoke one-to-one approach. Tier 1 accounts are essentially markets of one and have the greatest potential of turning into customers with the highest LTV.
These accounts, therefore, deserve as much focus and resources as possible. Assign each account with its own content plan and account manager. You will need to understand the organization inside and out.
- Who are the key stakeholders?
- Which ones do you know?
- Which ones do you need to know?
Tier 2 Accounts
These are smaller accounts that may not need as much research and/or don’t offer the same revenue potential as tier 1 accounts. The strategy will stay the same as in tier 1, but without as much personalization. So, instead of creating entirely new strategies, you can make do with tailoring existing campaigns with data gained from research.
Tier 3 Accounts
These are typically smaller accounts without the revenue potential of tier 1 and 2 accounts. You can use regular demand generation strategies with account-level targeting for them. It’s best not to invest a lot of time or money into these accounts as they satisfy the least number of ICP criteria.
Your ABM campaign should consist of a mix of all three types of accounts for the best results.
Strategy #3: Find points of contact in your targeted accounts
Regular cybersecurity lead generation campaigns try to target CISOs, CSOs, CTOs, and CIOs.
But while you can easily find all their titles and emails on LinkedIn, simply pitching them your product will not work.
CXOs today employ spam filters and caller IDs to block out the noise. Your ABM campaign needs to take the company’s social matrix into account before reaching the targeted decision-maker.
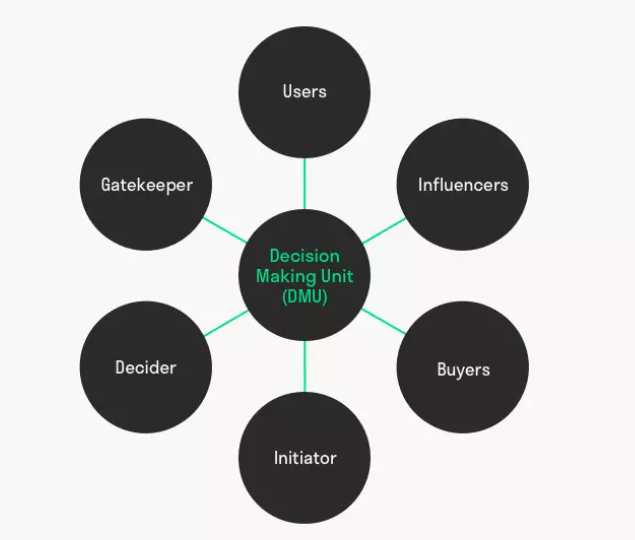
The social matrix consists of initiators, gatekeepers, influencers, decision-makers, blockers, and users — all of whom lead up to the stakeholder you are trying to reach.
The Initiators
The initiator is someone who recognizes the need for change within an organization. This can be a top-level CXO or a junior executive. An initiator, if present, is your best bet for making inroads into an organization because they are already aware of the need for change.
The Gatekeeper
The gatekeeper is usually an executive assistant. Many sales reps are quick to dismiss the assistant and go straight for broke, but, doing so can hurt your chances.
An executive assistant is often deeply tied to the CXO’s schedule, so giving them the cold shoulder is a bad idea.
Instead, it’s better to build a relationship with the assistant first as it can help you get an internal referral.
The Influencer
Is a junior executive who mines data and researches choices that the CXO needs to decide. Influencers do not have a direct say in the decision-making process. But the research they do helps determine what the CXO may go with.
Having the influencer on your side can greatly increase your chances of scoring a sale. They can introduce you to other key stakeholders and let you in on valuable information needed to hone your pitch.
The Blocker
The blocker is an influencer turn antagonist. They often go mute after a few follow-ups and might even stall your progress if they think your pitch isn’t up to snuff. Consider contacting at least 2-3 influencers (if possible) in each account to get around a blocker.
The Decision Maker
You’ll be most interested in approaching a CTO or a CSO since we’re running a cybersecurity lead generation campaign here. But, purchase decisions in large organizations are often complex and often involve several CXOs.
This is where your influencer contacts can prove useful. They can let you in on who is likely to weigh in on the purchase decision and what criteria they might use to make it.
The Buyer
Large organizations usually have dedicated staff for negotiations and selecting vendors. A buyer is responsible for negotiating terms and conditions, issuing the purchase order, and tracking deliverables.
The User
Refers to the group of people who the purchase is being made for. Users are responsible for post-purchase evaluation, bug reports, upgrades, and other feedback.
Again, your influencer contacts can prove invaluable to understanding user needs. This will be important to ensuring a good user experience and post-purchase satisfaction.
The following tools are best for identifying and targeting decision-makers:
- D&B Hoovers: Provides corporate databases and sales intelligence.
- Charlie App: A digital studio for creating personalized experiences.
-
Salesforce Einstein: A complete ABM solution offered by Salesforce.
Strategy #4: Create marketing material for each tier
Creating highly targeted and relevant content is a high priority in ABM as a personalized experience is at its core. Since personalization is a highly time-intensive process, your cybersecurity lead generation content should be mapped to each of the ABM tiers.
Tier 1 Accounts
Each account gets its own content strategy. Every piece of content is tailor-made to suit the account’s particular nuances. As much personal information should be used here as possible.
Personalization doesn’t mean creating everything from scratch. Feel free to repurpose old content with brand-specific updates if possible.
Tier 2 Accounts
Playing with headlines, visuals, and subsections to make the content look and feel more specific to an account can do wonders here without overinvesting. Be careful, though! The content you’re sharing will need to be evergreen. So freshen up those outdated facts and statistics regularly.
Tier 3 Accounts
Regular inbound marketing strategies with basic personalization added as and when required. Consider curating content from your resources into account specific packages. You can personalize the collateral with industry or technology-specific updates.
Conclusion
Cybersecurity solutions are in hot demand right now as many companies are working through a new way of life without prior experience. Remote working presents many security challenges that need unique solutions such as AIOps and MLOps.
This means that the cybersecurity landscape is becoming increasingly competitive. Your best bet moving forward is outwitting the market with hyper-personalized and smart marketing that helps deliver the right solution at the right time.
An account-based cybersecurity lead generation campaign can help you gain better insights into your prospect’s needs and reach out to them with content they’ll want to consume.
What are your thoughts on cybersecurity lead generation? Feel free to leave a comment below if you have any questions or thoughts.